When you remove technology from the office at any time, for any amount of time, and then connect it back to the network, you’re risking introducing a virus. For example, with ransomware, the attacker could be sitting on the device, waiting for it to reconnect to the network. Once reconnected, your whole system is ripe for the picking.
Cybersecurity breaches are expensive. The last thing you want to deal with upon returning to the workplace is losing trust with customers over a cyberattack.
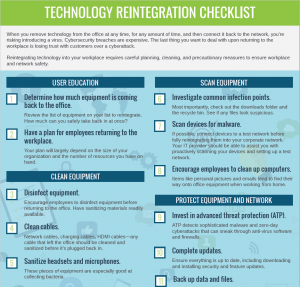
Reintegrating technology into your workplace requires careful planning, cleaning, and precautionary measures to ensure workplace and network safety. Here, we’ll share 11 tips to consider when reintegrating technology into your workplace.
User Education
Having a plan is an essential first step. To be effective, you need to make sure users know the plan and stick to it.
1. Determine how much equipment is coming back to the office.
Before you get started, take a look at the list of equipment on your list to reintegrate. How much stuff are you prepared to take in at once? Are there users that will require special assistance? What can users do to make reintegration easier?
2. Have a plan for employees returning to the workplace.
Your plan of action will generally depend on the size of your organization. Can you handle all employees returning at the same time, or does it make sense for you to have a gradual reintegration? You want to have a plan in place to properly reintegrate your equipment and quickly identify any issues that pop up.
Depending on how long employees have been working remotely, you also want to assess your network’s overall performance. Dust off the cobwebs, make sure everything is still intact, and test your speed and bandwidth.
Clean Equipment
When equipment leaves the office, you have no idea what happens to it. Any equipment returning to the workplace should be cleaned and sanitized before it comes back into the office. You don’t want a happy, healthy office to turn into a sick one the next day.
3. Disinfect computers, keyboards, monitors, etc.
Encourage employees to clean their equipment before heading to the office. Better yet, have sanitizing materials readily available when greeting employees as they return. Be sure to wash your hands often when working on other people’s equipment regularly and avoid touching your face.
4. Clean cables and auxiliary equipment.
Network cables, charging cables, HDMI cables—any cable that left the office should be cleaned and sanitized before it’s plugged back in. We often forget how often we handle these items. When you’re reintegrating equipment, you’ll be touching a lot of cabling. Make sure it’s clean.
5. Pay extra attention to headsets and microphones.
These pieces of equipment are especially good at collecting bacteria. They’re used near mouths and are often designed with holes and ridges that can catch germs. Encourage employees to clean these before they pack up their home office and return to work.
Scan Equipment
Before connecting any equipment to your office network, you need to make sure it’s clean from any harmful files, malware, and viruses. You don’t want to plug a computer in, then infect your entire network.
6. Scan devices for malware.
Malware is any type of harmful software. Examples of malware include ransomware, network viruses, and browser hijackers. Many types of malware can lie dormant on a device and wait for the right opportunity to strike, like when connecting a device to an expansive corporate network. If possible, connect devices to a test network before fully reintegrating them into your corporate network. Your IT provider should be able to assist you with proactively scanning your devices and setting up a sandbox or test network.
7. Investigate common infection points.
Most importantly, check out the downloads folder and the recycle bin. See if any files look suspicious. Be on the lookout for .exe files or any files with multiple extensions.
8. Encourage employees to clean up computers before bringing them back into the office.
When working remotely, we often blend our personal and professional lives. That means things like personal pictures and emails find their way onto office equipment. Encourage employees to clean up their workstations before bringing them back into the office.
Protect Equipment and Network
Once you’ve completed scanning the equipment and you have deemed it safe and clean, it’s time to make sure the equipment and your network remain safe for the long haul.
9. Invest in advanced threat protection (ATP).
ATP is a cybersecurity solution that proactively defends your business against cyberattacks. Using technologies such as machine learning, code analysis, and sandboxing, ATP detects sophisticated malware and zero-day cyberattacks that can sneak through anti-virus software and firewalls.
10. Complete system, manufacturer, and vendor updates.
Before allowing any equipment back onto your network, ensure everything is up to date, including downloading and installing security and feature updates. With remote work and bring your own device (BYOD) environments, you may not know when users last completed updates. Double-check that you have downloaded and installed all system, manufacturer, and vendor updates before allowing the device back on the network.
11. Back up your files.
Technology hiccups happen when you least expect it. If the equipment has been out in the field for a while, there’s probably essential data and files that you should back up before allowing the device back on the network. By updating your backups, you can ensure your important data is safe, regardless of the network or equipment.
We Keep Your Businesses Safe.
High Touch helps keep businesses safe with Cybersecurity, Data Backup, and Website Security solutions. Additionally, we can provide essential services for businesses interested in examining comprehensive technology solutions for a remote workplace.
If you need assistance or guidance for reintegrating equipment back into the workplace, contact us. We can help make things easier.